Europe proposes a very strict regulation that requires increasing the factory security of any device designed to be connected to the Internet
16/09/2022Some details from the new rules of the European Commission against cybercrime, 'Cyber Resilience Act', are beginning to be known. Among what has transpired is that the new regulation will force all manufacturers of potentially insecure products to increase it substantially and to provide more information to buyers about the level of protection of the devices they buy. This regulation will be of general application, and will affect all types of devices and systems, from the most basic such as a watch to the most sophisticated such as the software of any computer designed to be connected to Internet. All must comply with the provisions of the 'Cyber Resilience Act' to receive its approval and be able to be sold on the European market, and also, to avoid being subject to investigations and significant fines. In this sense, the proposed sanctions that are considered in the draft of the regulations could reach 15 million euros or 2.5% of the global annual income of the fined company. According to the European Commission in the presentation of the consultation carried out for the elaboration of the 'Cyber Resilience Act', "the new regulation aims to respond to the needs of the market and protect consumers from unsafe products by introducing standards common cybersecurity standards for manufacturers and sellers of tangible and intangible digital products and ancillary services.
[ ... ]How to sign a PDF document with electronic signature?
24/06/2021When a document needs to be signed by one or more people, the usual thing, until now, has been to print it and stamp by hand the necessary signatures to validate or make its content official. This requires paper, printer, ink, but above all access to the document by all signatories, which is not always easy due to geographical location, availability, timing, etc. With teleworking on the rise and a growing globalization of business, these drawbacks have become more evident than ever, although they have found a quick and effective solution in electronic signatures. What is an electronic signature for? The electronic signature is a digital validation system for documents that unequivocally identifies the signatory. The electronic signature is assimilated to the handwritten signature and therefore its digital stamping on a document gives it the same validity, as it would have had with a handwritten signature. What are the advantages of electronic signatures? Electronic signatures simplify document management processes that require the validation of documents such as pdf signatures, facilitating remote signing by one or more people regardless of where they are located, or the situation or time of day they receive them. This flexibility contributes to the efficiency and agility of this type of procedure and being a secure signature system, it is suitable and useful in many areas related to business management, administrative management, e-commerce, informed consent and many other procedures. In addition to the versatility, practicality and security of the online PDF signature, we must also point out, as a great advantage of this process, its contribution to paperless. How to sign electronically? The electronic signature is easy to implement through tools specifically designed to guarantee not only the correct validation of the cryptographic signature or signatures included in a PDF document, but also that it cannot be altered and that all the necessary signatures required by each situation can be added. Within the framework of this type of tool, the most advanced ones, in addition to being compatible with any browser and accessible from any type of device - computer, tablet, Smartphone,... -, make it easy to convert PDF any Word, Excel, JPG, PowerPoint... file for signing. They also allow users to request a verifiable digital signature, view the properties of the digital signature and send the document directly by email to the signatories and once signed, forward it to all parties to download it. In addition, to guarantee the privacy of the documents and the security of the online signatures, these transfers are made through encrypted files with TLS encryption. Also, when we sign documents using this type of tool, they offer the option of including a LTV (Long Term Validation) time stamp that certifies the validity of the signature in the long term. For all these reasons, tools for signing PDF documents with electronic signatures are now a must for companies and businesses in all areas where process optimization, security and sustainability are a priority.
[ ... ]49% of consumers are willing to favor brands that explain data usage in AI interactions
17/04/2024Artificial intelligence (AI) has become a fundamental tool for companies striving to provide personalized and efficient customer interactions. However, a new report reveals that the lack of transparency in data usage by brands is affecting consumer trust. According to Twilio's fifth 'State of Consumer Engagement Report', based on a global survey including over 4,750 B2C executives and 6,300 consumers across 18 countries, 49% of consumers would trust a brand more if it disclosed how it uses data from AI-driven interactions. The report also highlights that, although 91% of brands claim to be transparent with their customers about AI usage, only 48% of consumers agree. In this context, data protection emerges as a priority for consumers, with six out of ten indicating it's the best way for brands to earn their trust. This data security concern is shared by, the 40% businesses globally that considerate important to find a balance between security and customer experience as one of their most pressing challenges. AI-driven customer experience for brands AI-driven personalization is a key strategy to enhance customer relations. The report points out that companies adopting personalization experience a significant increase in consumer spending, averaging 54% more compared to those that don't. AI not only helps bridge the customer experience gap but also provides additional benefits, such as better data-driven decision-making and increased customer satisfaction. However, the report highlights that many companies face difficulties in activating customer data. Globally, only 16% of brands fully agree that they have the necessary data to understand their customers.
[ ... ]
Audio/Video Cables
Do you want to enjoy superb picture quality and high-fidelity audio? Always use a cable designed and manufactured specifically for this purpose. These cables will protect the signal from any external interference that may alter it and will provide you with the sound and video quality you are looking for. In our wide selection of A/V cables for analog or digital signals, you will find audio cables, video and audio cables, and video cables for stereos, projectors, televisions, speakers, antennas, headphones, DTT or Satellite receivers, etc.
[ ... ]Alcatel
AlcatelIt is not easy to summarize Alcatel's long history as a global telecommunications giant. Alcatel, now called Alcatel-Lucent, has been evolving and innovating in the telecommunications field for more than 100 years. Undoubtedly, Alcatel stands out for its telecommunication services. Their presence in the fixed home phone market was quite significant a few years ago. Nowadays, they focus their innovative energy on creating high-quality smartphones and tablets with attractive and increasingly functional designs. Today, Alcatel plays a major role in R&D activities in France, its country of origin.
[ ... ]How to change the IP address?
How to change the IP address? We will explain step by step how to change your IP to be able to browse safely and anonymously on the Internet. The Internet is like a great highway and to "drive" on it, we must get on the road equipped with a computer, tablet, smartphone... with a license plate. This "license plate" is what is known as IP address and for many and several reasons, but mainly for security and/or privacy reasons, we may be interested in changing it. What is my IP? In order not to put the cart before the horse the first thing we must do to know how to change the IP of the computer is to find out what the IP of our connection is and verify that the change has been made correctly at the end of the process. Finding out what your IP is is as simple as visiting Cuál es mi IP (What is my IP). By accessing the page, without the need to download or run any program, our tool will automatically display your IP address data on the screen. This address is also useful to know if you want, for example, to configure online services such as servers, FTP, games, ... and it consists of a numerical combination. This address is unique and public and is the one that identifies us on the Internet to the websites we visit and other users. Nobody can browse the net without an IP address. The IP is assigned to us by our Internet Service Provider (ISP) and as this address is exposed on the network it is known as public IP, as opposed to the private IP of our local network, which only we can know. What is my public IP and what is my private IP? How important are they to change my IP? Our computer or any other device connected to the Internet has two IP addresses, a public IP address, and a private IP address. The public IP, as we have seen, is the one that identifies us to be able to surf the Internet (imagine driving on a highway without a license plate... we would be stopped and banned from driving!) This public IP is linked to our connection and, therefore, all devices connected to the same router have the same public IP. On the other hand, the private IP is the one that individually identifies each device in our private or home network. In this local network, each computer has a private IP address that serves to differentiate it from the rest of the computers and devices connected to the router. In this way, any request for data that comes from or is sent to a device is identified by the router so that it collects or sends the corresponding data to that device. So, which IP address should I change? Private IPs are not accessible from the Internet, while public IPs are and allow us to track our location, data, and Internet activity, including the pages we have visited or the time we have spent on each of them. So, to improve our security and privacy on the Internet, we can change the public IP, or if we prefer, hide our IP. Doing so is not complicated and now we will explain how to change the IP, but first, you must make sure if your IP address is a dynamic IP or a static one, as it depends on it that you can manage to change the IP on your own or require the intervention of your Internet Service Provider (ISP). How do I check if my IP is dynamic or static before changing it? IP addresses can be static or dynamic. In both cases, these addresses are assigned by our Internet provider and the difference between them is that in the case of the static IP, IP addresses can be static or dynamic. In both cases, these addresses are assigned by our Internet provider and the difference between one address and the other is that in the case of the static IP, the address assigned is permanent for a device or router, while the dynamic IP changes every time that device or router connects to the Internet. Usually, the IP address is dynamic, but you can check it through our free tool to find out what is your IP address on our website. Remember that you do not need to download any program or run any application. Simply access cualesmiip.com and the home page will show your IP address, indicating whether it is a static or dynamic one. If it is a static IP address, you will have to contact your Internet Service Provider (ISP) and request the change or use a VPN service as we will explain below. But if it is a dynamic IP address, the change is easy and you have several alternatives for doing so. How do I change my public IP? The easiest way to change the IP address if it is a dynamic one is to turn the router off and on again. This will change the public IP and when you browse again you will do it with a different IP address than the one you had before turning it off. The tricky part of the situation is that the new address, like the previous one, will continue to be exposed on the network and if you want to change it again you will have to turn the router off and on each time. However, it may happen that despite doing so, this does not work and the IP address does not change. This happens because in certain circumstances Internet Service Providers (ISP) establish a certain period before which IP addresses cannot be changed. How to change my IP with a VPN? If you are looking for a solution that does not force you to be aware of turning your router on or off and that also offers a permanent solution that contributes to your online security and privacy, VPNs are already the most effective solution for changing your IP. VPNs are services designed to hide the IP address, whether you connect with a static IP address or a dynamic one, using that of an intermediate server, in such a way that the IP address is masked, appearing to the public as a different IP permanently. As this new Public IP belongs to the VPN server, none of our data is exposed and whoever traces the address will only reach that server, without being able to access any data about our connection, navigation, and identity on the network. VPN vs Proxy Proxy servers act in a similar way, although VPNs have the added advantage that they encrypt all data from the beginning to the end of the communication so that the impossibility of tracing data is 100% guaranteed. Proxy servers do not have this function and therefore your connection may still be susceptible to falling prey to cybercriminals. In addition, most proxy servers, unlike VPNs, must be configured manually and even, in some cases, individually in each browser. How do I know if my IP has been changed? And now that you know how to change the IP, you can test and check whether it went well by comparing your new IP address with the one you had before. If everything went well, you will see that the numbering is different and therefore your IP has been changed.
[ ... ]Telegram incorporates chatbots into Telegram Business accounts
03/04/2024Telegram Business has announced the addition of chatbots among its features aimed at streamlining communication between companies and their clientele. The new automated assistants on this instant messaging application are designed to provide information automatically in response to predictable inquiries. This recent development was announced through the company's official blog, where Telegram also explained that the chatbots also have the option to provide links that direct customers to booking or order tracking. Additionally, these new automated assistants from Telegram Business are also capable of offering welcome messages and absence notifications, useful for informing customers, for example, about holiday closures. Telegram explains that thanks to this new feature of Telegram Business, user companies will be able to enhance their brand presence and foster lasting relationships with their customers by leveraging the power of automation along with personalized communication.
[ ... ]
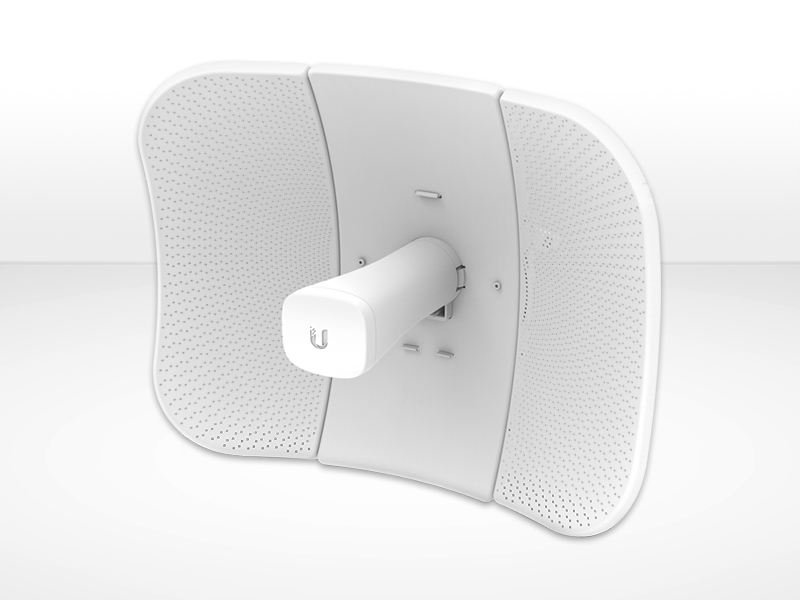
Access Points
In our store, you will find multiple options so that you are not left without coverage in any corner. With an access point, for example, you can cover all the rooms of your home or office farthest from the router with a Wi-Fi signal and create a local area network that will ensure your Internet connection, wherever you move.
[ ... ]Apple
AppleThe fact that Apple is possibly and currently the most complete and well-known technology company in the world, seems a no-brainer. Many articles must have been written about the origin and creation of the Apple brand and its history, back in 1970, with curious facts such as the fact that it was created in a simple garage, with few means and by some electronics freaks. Who hasn't heard of Steve Jobs, a visionary who, together with his two colleagues at the time, revolutionized the world and certainly changed history in many ways. At least, that of technology. Apple, from the garage to the present day. Over the years it has managed to become a technology giant with an impressive number of products, manufactured with technological quality and cutting-edge design.
[ ... ]
Cookies
A cookie is a file that is downloaded to your computer to access certain web pages. Cookies allow a website, among other things, to store and retrieve information about the browsing habits of a user or their equipment and, depending on the information they contain and how you use your computer, they can be used to recognize the user. However, this only means obtaining information related to the number of pages visited, the city assigned the IP address from which you accessed, the number of new users, frequency and recurrence of visits, time of visit, the browser or the operator or terminal type from which the visit takes place. In no event will data be obtained about the full name or address from which the user is connected. The cookies used on this website and the specific purpose of each one are: UTMA Cookie: We use this cookie to count how many times a unique user visits the site. UTMB Cookie: We use this cookie to calculate how long a user stays on a page. UTMZ Cookie: This cookie stores the visitor's origin, the path followed to access the web, either the direct access from a link on another website, from an email link using certain keywords in a search engine, through a display campaign, or through an AdWords ad. UTMC Cookie: The current JavaScript code that Google Analytics uses does not require this cookie. This cookie is used, along with the utmb cookie, to determine if after more than 30 minutes on the same page a new session should or should not be established for the user. This cookie is still written to ensure compatibility with the websites where you installed the old urchin.js tracking code. PHPSESSID Cookie: We use this cookie to identify the relevant user. You can allow, block or delete cookies installed on your computer by setting your browser options. You can find information about how, in relation to the most common browsers, on the links listed below: Explorer: http://windows.microsoft.com/es-es/windows7/how-to-manage-cookies-in-internet-explorer-9 Firefox: http://support.mozilla.org/es/products/firefox/cookies Chrome: http://support.google.com/chrome/bin/answer.py?hl=es&answer=95647 Safari: http://support.apple.com/kb/ph5042 Please note, however, that there is the possibility that disabling any cookie may prevent or hinder navigation or the provision of services offered on this website.
[ ... ]
All-in-one computers
All-in-one PCs have both the capacity and intelligent performance of a desktop computer and the elegance of a modern and minimalist design. Save space and avoid having cables on your desk with these all-in-one PCs designed to adapt to your needs. In our store, you will find different models of all-in-one PCs with and without OS. Windows and Apple all-in-one PCs.
[ ... ]Conceptronic
ConceptronicFor more than 20 years since its creation, the Conceptronic brand has managed to achieve a prominent position within the consumer market for any product that stores, retrieves, manipulates, transmits or receives information, well, what is commonly known as an ICT product. The evolution of this Dutch company, grows in parallel to the development of new solutions with the latest technology and elegant designs to meet the personal demands of users, betting mainly on a range of products with a specific focus on the areas of connectivity and mobility.
[ ... ]A new FakeUpdates campaign targeting WordPress sites has been detected
20/03/2024Over the past few weeks, a new wave of the FakeUpdates malware, also known as SocGholish, has been detected, aimed at WordPress websites. The objective is to lure users into downloading remote access trojans, allowing attackers to take control of their systems. Since its emergence in 2017, FakeUpdates has been one of the most recurring malicious software in the cyber threat landscape. It has previously been associated with cybercriminal groups like Evil Corp, who monetize its use by selling access to infected systems. In this new campaign, cybercriminals are using JavaScript to target WordPress web pages, compromising compromised administrator accounts to introduce altered versions of WordPress plugins. These adulterated versions deceive users into downloading remote access trojans, granting attackers full control over infected devices. What is the most popular type of malware? In addition to the FakeUpdates attack, the threat index from Check Point Research, whose researchers have warned about this new attack, reveals around 200 suspicious content websites directed by ransomware groups. They utilize double extortion tactics to pressure victims into paying immediate ransoms. These attacks have impacted many companies, with the Lockbit3 ransomware being the most utilized by cybercriminals, followed by Play and 8base. The most exploited vulnerabilities by malicious actors include 'Web Servers Malicious URL Directory Traversal,' 'Command Injection Over HTTP,' and 'Zyxel ZyWALL Command Injection,' affecting numerous companies worldwide and allowing attackers to access and manipulate files or execute commands on compromised systems. In Spain, despite a 7% decrease in malware attacks in February, the most sought-after malware includes FakeUpdates, Qbot, and Pandora. In the case of FakeUpdates, it has affected 11.9% of companies in Spain. Mobile Malware In the realm of mobile devices, Anubis remains the most utilized malware in Spain, followed by AhMyth and Hiddad, all designed to compromise the security and privacy of Android device users by collecting confidential information and executing malicious actions.
[ ... ]How can I hide my IP?
Accessing the Internet involves connecting our computer, smartphone, tablet, etc. to a communications server that is responsible for providing access to the network. This connection involves the identification and exchange of data about our identity, IP address, and online activities that are recorded forever as a trace of our navigation. Can I be tracked through my IP address? Yes, it is possible to trace an IP address and for those who consider privacy a priority, this is a major problem because, in addition to being exposed throughout the network, the increasingly intensive use of the Internet has led to this type of data becoming an object of interest for cybercriminals seeking personal or confidential information that can be used for their benefit. To safeguard against all this, there are several methods to hide the IP address, ensure our online privacy, improve our security on the Internet, and prevent anyone from knowing what pages we visit, the time we have spent on every connection, or what we are downloading. What are the advantages of hiding my IP? Apart from everything related to privacy and security already mentioned, hiding the IP offers different advantages for users in multiple circumstances: There are IP hiding services that prevent IP geolocation when we travel and allow us to connect to the network as if we were doing it from our own country, overcoming, for example, any network access limitations that may exist in the place where we are. We will be able to download files anonymously avoiding that the rest of the users can see our IP location. If our IP is not "in sight", the possible limitations and blockages of the Wi-Fi network and even of our ISP (Internet Service Provider) disappear. Thanks to the data encryption system of the most advanced IP hiding services, our vulnerability in connections to public Wi-Fi networks is minimized. When the system detects a location different from the real one, this can give us advantages to buy in online stores with different offers according to the country or to avoid the blocking of games, maps, and online game add-ons that may have restrictions on our location. How can I hide my IP? IP hiding is achieved through the use of specific services and tools to hide the IP and encrypt our traffic, those services allow us to hide the real communications we make during our navigation. Besides those techniques that are based on the modification of network protocols and require certain skills to carry them out, there are several technologies within the reach of all users: VPN or Virtual Private Network Proxy or Web proxy Tor Public Wifi How to hide the IP address with a VPN? VPNs are services that connect us to the Internet through intermediate servers, in which our original IP address is " masked " by the IP address of that secure server. This concealment ensures that anyone tracing our connection will only see the IP address and location of the VPN server, but not our own. In addition, to safeguard our activity on the network, VPNs use tunneling and data encryption, encrypting the information we exchange with the VPN server, hiding it, and preventing third parties from being able to read it during its transit. The security of VPN connections is determined by proprietary VPN protocols, based on different standards and encryption and authentication methods, which depend on each developer. The range of options is wide and this allows us to choose between, for example, options that prioritize speed over security, options that do the opposite, options with a greater or lesser degree of reliability, etc. VPN applications always run in the background and do not hinder browsing. How to use a proxy server to hide the IP address? Unlike VPN services, proxy servers focus their activity solely on hiding the IP, without performing any type of concealment on our network traffic or any other data that could reveal our identity. Proxy servers act as intermediaries between our device and the destination server to which they transmit our requests on our behalf. Therefore, our IP will be hidden and the only one they will see will be the proxy one. There are different types of proxy services, from the simplest ones that only help us to hide the IP to others with extra functionalities such as blocking cookies, scripts, and other files hosted on websites and sent to the user. Browsers or applications based on the HTTP protocol offer the manual proxy configuration function so that we can indicate the proxy web address and port to which we want to connect before browsing. In this way, any activity that we perform through that browser will always be routed to the proxy. Alternatively, you can also opt for the automatic proxy format that searches through DNS or DHCP for the URL from which to download the wpad.dat file that runs and allows the proxy connection with automatic authentication on your computer. How to hide your IP with Tor? Tor is a free software developed to ensure anonymous browsing of users on the Internet. To mask the IP Tor uses a network of volunteer computers or nodes through which it redirects our traffic and encrypts it before it reaches its destination. At least this redirection goes through three of these nodes, achieving repetitive re-encryptions so that any possible clue about our identity disappears. In this process, Tor assigns a random and geographically different IP to our connection so that the location by third parties is impossible (if you are curious to know the IP you have been assigned you can check it through our tool). This system allows different configurations depending on whether we are using a firewall, if our ISP is blocking Tor connections or if we navigate through proxy for example. Can I hide my IP with a public Wi-Fi connection? The answer is yes. A public Wi-Fi network can also be used to hide our IP address, although if we do not have it constantly at our disposal, the IP hiding is limited to the time we have access to a public network. As this type of network is a connection shared by many other people, this makes it impossible to trace a particular user or identify them on the destination server. However, it is precisely this general access that also makes us more vulnerable. And although through a connection to a public Wi-Fi we will solve the issue of IP hiding, security will never be total, because being an open network, we can be exposed to the will of hackers and other threats, including malware and viruses. And if I want to hide my IP address, how can I change it? It may also be the case that instead of masking the IP all we need to do is change our IP address at a given moment. Then, the solution is as simple as disconnecting the modem from the power supply and restarting it after a few minutes. In that time, if your IP address is dynamic (you can check it through the network connections tab on your computer), it will be deleted and your Internet provider will give you a new one. To make sure that everything went well, we recommend doing something as simple as writing down the IP address before turning off the router and checking it again once it is up and running again. Another possible way to achieve the same result if you have a smartphone with a data plan is to turn this device into a wireless access point to which you can connect your computer, thus hiding your usual connection. There are many options to hide the IP or to change it and now that you know how each of them works you will be able to decide which one suits you best.
[ ... ]WiFi Security: Assessment of threats in wireless networks
08/03/2024Wifi connectivity has gone from being limited to restricted environments to becoming omnipresent in virtually every aspect of our daily lives. The ability to connect to the Internet from anywhere, be it at home, in a café, at work, in public spaces, or even in-flight, has enhanced the convenience in our daily lives. Moreover, the expansion of Wifi networks and the use of new manufacturing technologies now allow the interconnection of devices, leading to the significant rise of the Internet of Things (IoT) and providing users with more comprehensive control over their digital environments. However, this proliferation of Wifi networks has also given rise to new threats that require careful evaluation and effective security strategies to ensure secure and risk-free Wifi connections for our data and information. Common Wifi security threats include data interception Man-in-the-Middle (MITM) attacks One of the fundamental challenges in Wifi security is preventing MITM attacks, where an intruder inserts themselves into the communication between two parties, compromising the integrity and confidentiality of sensitive data such as passwords and financial information. Spoofing of access points Hackers can create fake Wifi networks that mimic legitimate ones to attract unsuspecting users. Once connected to these malicious networks, our data can be captured by cybercriminals who may sell or misuse it for illicit purposes. Tips for achieving a secure Wifi connection: Strengthen authentication and use security protocols Prioritize strong encryption for networks to protect confidential information transmitted through it. WPA (Wifi Protected Access) encryption uses stronger algorithms than its predecessor, WEP (Wired Equivalent Privacy), making it more difficult for hackers to intercept and decipher data. Advanced security protocols like WPA3 provide individualized data encryption and advanced two-factor authentication (2FA) methods, adding an extra layer of security by requiring additional verification. Device management Properly manage and monitor devices connected to Wifi networks to minimize risks associated with the large number of connected devices in homes and businesses. Regularly update the router firmware and all connected devices to address potential vulnerabilities. Segmentation of the network to separate critical devices from less secure ones also helps mitigate the risk of threat propagation. Secure Router Configuration The router secure configuration is what will ensure the robustness and overall security of a wireless network. The router, being the first point of contact for devices connected to the Internet, acts as the first line of defence against potential attacks. For this reason, it is important to understand that the proper configuration of the router not only guarantees a stable and efficient connection but also establishes a protected environment that safeguards the integrity and privacy of our data. How to configure the router securely? To ensure a correct and secure configuration of the router, it is recommended to: Change the default username and password of the router, as these are easily accessible to attackers. Use strong passwords containing a combination of letters, numbers, and special characters. Disable remote administration to prevent cybercriminals from accessing the router externally. Enable WPA2 or WPA3 encryption instead of the outdated WEP for enhanced network security. Optionally, disable SSID broadcast to make the network less visible and harder to detect by hackers. Keep the router firmware updated to address vulnerabilities and improve overall device security. By following these steps, you will strengthen the security of your wireless network and reduce the chances of experiencing unwanted attacks or intrusions.
[ ... ]Genius
GeniusGenius is a reputable manufacturer of computer-related electronic products and accessories. Genius is a Taiwanese company founded in 1983 that has become one of the leading international peripheral brands by bringing people closer to the digital world. Genius designs mice, keyboards, stylus, headsets, speakers, webcams and gaming devices that provide a great user experience. Its peripherals have the best price-performance ratio on the market and are designed for both home and professional use.
[ ... ]Ip Location, the tool to know my ip location
If you need to check what location your internet provider is sharing with the websites you visit, with our IP locator you can instantly geolocate your IP address or any other that you enter manually. To geographically locate the IP address, you only need to be connected to the internet. If you use VPN software or connect through a proxy to locate IP address you can also use our tool. None of the data generated by the IP locator is stored in our system. @Mapa@ How can I hide my IP address so that it cannot be traced? To anonymously browse the Internet and avoid being located through the IP of your connection, there are two basic ways to do it. The first is to hide IP so that no one will be able to track our presence on the network or access our browsing data and the second is to change IP and browse through another IP address whenever we need to. Why do I need to locate my IP geographically? Locating your IP geographically is the best way to find out what data our ISP shares about the location of our connection. Depending on this location. a website whose URL is ".com" will change to "/es" if we connect from Spain, for example, and some tasks related to the sending of forms will be simplified, as they will be automatically pre-filled with some data such as your country or city, depending on your geolocation IP. As users with a geolocation IP tool such as the one we offer in Cuál es mi IP, we can manually enter an IP address and find out, for example, from where we have received a fraudulent email, if we have had access before, of course, to the IP address involved Can anyone find out my home address with an IP geolocation tool? By using a tool to locate an IP address, you can trace the IP and geolocate it through coordinates on the map, but the specific postal address is never provided. This is because our IP address is not ours, but rather our Internet Service Provider's (ISP's). So what data can they find out about me with IP geolocation? When locating the IP geographically. the only information about us that is provided is the country and city from which we are connecting, since the GPS coordinates of altitude and latitude that are shown correspond, in reality, to those of the headquarters of the company that is offering us the Internet connection service. The reason behind this is that all data related to the actual geographic address of the device used to access the Internet, i.e. our router, is not public and belongs to our ISP, which can only disclose it by court order. Why are companies interested in locating my IP address geographically? Information is power and for a company to know from where its potential customers connect is an important advantage to design marketing strategies aimed at the customer profile of a particular geographical area or country. In addition, in terms of anti-fraud, e-commerce companies can improve card payment security by identifying payment attempts from suspicious IP addresses. What is an IP address? An IP address is a special numerical combination assigned to an internet-connected device to be identified on the network. All intelligent devices need an IP address to access the Internet and interact on the network. Each device connected to the Internet has its own an individual IP address. When we access the Internet, the servers recognize our device through its IP address, allowing the two-way communication with the recipient. As we are identified with our IP address, the rest of devices can order a return response, without mistake the sender. Making a simile, an IP address would be the address that we use to write on the back of an envelope. This information identifies us as issuers and also as recipients of the return answer. To make possible this data exchange, the IP protocol was established as a set of universal rules for all the Internet operations. That means that all devices connected to Internet or to a home network, "speak" the same language and they are able to communicate each with the others. There are two types of IP address, the external IP and the local IP: • The external IP or public IP is the numerical combination address assigned to us by our Internet service provider (ISP). This public IP identifies us as Internet users when we are connected. If you want to find the IP of your computer, your tablet or your Smartphone, you can find out this immediately by accessing the home page of “What is my IP” or using our speed test service that, in addition to this information, will inform you about the quality of your Internet connection. • The local IP address or internal IP is the one the router assign to all the devices connected to him and identifies each of these devices, individually, in the home network. How to locate an IP address? If you want to know how to find out where an IP address is from, you should know that it is not always easy to find out the IP origin of a connection, because there are different systems to hide the IP. Some users use these systems for security reasons or to simulate, for example, their IP location in another place and thus have access to Internet services not enabled in the place where they are located. Now, if the user does not use any resource to mask the IP, find out the IP of the computer or any other device connected, for example, to our website, it is as simple as use IP geolocation services such the one offered in “What is my IP?” and you will immediately find out the IP origin of any computer that you are interested in track. Knowing the IP location of our clients is an advantage when we are designing, for example, our marketing strategies and a good tool, also, to improve network security, as it allows us to locate suspicious IP addresses. In addition, with the IP geolocation service you can also verify the location that your Internet provider shares about you. It should be clarified that this location provided by IP geolocation services is never the specific address of our home or where we are located. The data actually are from the operator node in our area that is offering us the connection service to the internet network Therefore, the geolocation information will be the country and city from where the connection is made, but not the address where the user is located, because this specific tracking of the user address is protected by law and this data can only be provided by court order.
[ ... ]
Antennas
Find here the perfect antenna to improve your wireless network coverage, attract Wi-Fi signals to your devices or connect to an outdoor network. In this section, you will also find converters, indoor TV antennas for DTT, and outdoor antennas adapted to the new UHF standard with integrated 4G/5G filters.
[ ... ]Kensington
KensingtonAt Kensington, they know that for many people the computer is of vital importance. Whether you use your computer for work or simply have photos of important moments stored there, security should be one of your top priorities. For over 35 years, this brand of computer accessories has been a world leader in computer locks and security systems. It is headquartered in California. Kensington is a designer, marketer, and manufacturer of branded products for businesses and academic institutions. Their consumer protection lines are also popular. Their products are sold in more than 100 countries around the world.
[ ... ]
Legal Advise
This website, prepared solely for information purposes, is owned by Dommia Design Studio SL, hereinafter Dommia. Its contents are protected by intellectual property laws are expressly forbidden to reproduce (in whole or in part), copy or distribution without the express written permission of Dommia. Dommia assumes no liability whatsoever arising from the information on this site and reserves the exclusive right to modify and / or delete at will and without notice, the information contained in it. Dommia Design Studio SLc/Lepant, 326, entlo. desp.308025, BarcelonaCIF: B66445081Registered in the Mercantile Registry of Barcelona Volume: 44619, Folio: 176, Page: 461387, Inscription: 1
[ ... ]
Desktop computer
If you want to buy a desktop computer, you are in the right place. We have a wide variety of models with different configurations for business, gaming, video editing, 3D rendering, etc. You can also design your desktop PC to your needs. Choose the components you need and build your machine.
[ ... ]What is Worldcoin and what does scanning the iris involve?
04/03/2024Worldcoin was introduced in summer of 2023 as a revolutionary project with the mission of creating a 100% secure digital identity, essentially a kind of fortified "digital passport," based on the verification of a unique and non-transferable element inherent to each human being—the iris. According to its developers, World ID will help distinguish human online activity from that generated by machines. In the first phase of the project, the creation of this secure digital identity is planned for 2 billion humans. To make this possible, Worldcoin has called on the global population to scan their iris. In return, Worldcoin compensates participants with a few tokens of its successful cryptocurrency, WLD, which has quadrupled in value within a few weeks of its initial launch. The payment in WLD tokens is not coincidental; it is part of Worldcoin's strategy, aiming to leverage the new digital passports to create a comprehensive ecosystem that provides universal and equitable access to advanced financial services for the entire global population. To achieve this, they encourage "iris sellers" to use the Worldcoin cryptocurrency on its fee-free blockchain, unlike Bitcoin, Ethereum, or other cryptocurrencies that do charge transaction fees. How does Worldcoin work? Worldcoin aims to address the issues of bots, rapid creation of fake identities, and content with artificial intelligence. It is designed, according to its developers, to provide every individual in the world with a unique digital identification. Additionally, Worldcoin promises to ensure the financial inclusion of each person in a fair and equitable ecosystem through a universal basic income. Users receive this income in exchange for allowing their iris to be scanned. To create the secure digital passport with Worldcoin, users must undergo an iris scan, which serves as proof of humanity and a unique identity on the blockchain. This process ensures that the individual on the other side of that identity is a human and not a fake profile created with artificial intelligence. In pursuit of the success of their proposal, the company offers users a small amount of their own Worldcoin tokens in exchange for iris scanning. The initial incentive of receiving free cryptocurrency, in the form of a universal basic income, is emphasized by Worldcoin advocates as the basis for the inclusive and universal nature of their initiative. This approach allows anyone to scan their iris, and the WLD tokens received in return can assist people without access to traditional financial services in starting to save and invest. How to Scan the Iris with Worldcoin? The registration process with Worldcoin involves scanning the iris with an orb, the central hardware device of Worldcoin developed by Tools for Humanity. The orb is spherical and processes all the information. Currently, Worldcoin has installed orbs in different countries, including Spain, where users can scan their iris in exchange for Worldcoins. To do this, it is necessary to download the Worldcoin mobile application, World ID, generate a QR code with it, and display it in front of the orb. The orb, upon recognizing it, will scan the user's iris, while a Worldcoin collaborator remotely oversees the operation. The orb takes less than a minute to perform the scan and validate the subject's identity. In exchange for their iris, the user receives a unique number called "IrisHash" and a cryptographic wallet with Worldcoins. "This digital passport is accepted as proof of unique humanity, which people can use in the digital world without the need to share any other data," assure its developers. What happens with my scanned iris in exchange for Worldcoins? Once the iris scan is completed, and digital identity is granted to the user, Worldcoin assures that the orb quickly eliminates the images unless the user requests their preservation. Only the set of numbers called "IrisHash" is stored for identification, without any additional biometric data. Worldcoin also commits to ensuring that users share only the necessary information they wish to share, providing verification options through linked devices or the additional facial authentication orb for high-security cases. Despite these commitments, the collection of biometric data through iris scanning for the unique proof of humanity continues to raise significant questions regarding privacy and information security. Some countries such as Brazil, France, India, or Kenya have halted Worldcoin's iris scanning. How much do you get paid for scanning your iris? Worldcoin pays 25 WLD for scanning your iris, which, according to the cryptocurrency's exchange rate in February 2024, has translated to an average of between 50 and almost €160 for iris sellers, depending on the value of Worldcoin on the day they scanned their iris. At the beginning of February, the value of each WLD unit was around two euros, and by the end of the month, it had risen to nearly seven euros. What can I spend my WLD on? 'Iris sellers' have the freedom to use their Worldcoins from the moment they receive them. They can exchange the payment for other cryptocurrencies, withdraw them in euros from a specialized ATM, or hold onto the tokens in the hope of an increase in their value. Additionally, WLD payments are already accepted on platforms such as Discord, Shopify, Minecraft, Telegram, Mercado Libre, or Reddit, among other places. Who is behind Worldcoin? Worldcoin bears the stamp of two innovative minds: Sam Altman and Alex Blania. Altman is the CEO of OpenAI and a key figure in artificial intelligence development, leading projects like ChatGPT. Blania, on the other hand, is the co-founder of Tools For Humanity, contributing his experience in creating technological tools for a more equitable economic system to this new and successful cryptocurrency.
[ ... ]
HomePlug Networks
With these HomePlug networking devices, you will find it very easy to bring the optical fiber and Wi-Fi signal to any place in the house. Using the electrical network of your home, you will be able to expand the area of action of your router and create additional access points without losing the signal or the quality of the bandwidth you have subscribed to.
[ ... ]
Privacy Policy
Esta política de privacidad aplica a todos los contenidos de este sitio web y que sean publicados por Dommia Design Studio. Si usted tiene alguna consulta sobre cómo usamos su información personal, por favor contacte con nuestro responsable de privacidad en [email protected]. Según lo establecido en el RGPD (Reglamento (UE) 2016/679), les proporcionamos la Información Detallada de Protección de Datos que se expone a continuación: Responsable: Dommia Design StudioRazón Social: Dommia Design Studio SLC.I.F.: B-66440581Dirección: c/ Lepant, 326, Entlo, Desp 3 - 08025 - BarcelonaTeléfono: 936 241 455Correo Electrónico: [email protected] Inscrita en el Registro Mercantil de Barcelona Tomo: 44619, Folio: 176, Hoja: 461387, Inscripción: 1 Información que recopilamos y con qué objetivo Esta sección detalla la información que podemos recoger sobre usted. Explicamos por qué y cómo lo utilizamos en secciones posteriores. Información que obtenemos a través de cookies y herramientas similares Utilizamos cookies (y tecnologías similares) y herramientas de análisis en nuestros sitios para recopilar información sobre usted. Esta información se puede utilizar para mejorar el rendimiento del sitio y mejorar la experiencia de usuario. Proporcionamos información detallada sobre cookies y tecnologías similares dentro de nuestra Política de Privacidad; algunos ejemplos incluyen: Su ubicación: utilizamos cookies para mostrar información del lugar más relevante para su ubicación. Su uso: utilizamos cookies para entender como nuestros clientes utilizan nuestros sitios. El dispositivo: utilizamos cookies para entender el tipo de dispositivo que está utilizando para mostrarle la mejor versión del sitio. Si desea administrar sus cookies, siga las instrucciones de la sección "Cómo gestionar las cookies" dentro de nuestra Política de Privacidad. Información que obtenemos a través del formulario de contacto Datos de contacto: nombre y correo electrónico. Web Beacons Utilizamos web beacon en nuestras páginas web y nuestros correos electrónicos. Cuando enviamos correos electrónicos a los miembros del boletín de noticias, podemos hacer un seguimiento del comportamiento como quien abrió los correos electrónicos y quien hizo clic en los enlaces. Esto nos permite medir el rendimiento de nuestras campañas de correo electrónico y mejorar nuestras características para determinados segmentos de miembros. Fundamentos legales para el procesamiento Solo tratamos información personal cuando tenemos su consentimiento de usuario: es decir, cuando nos ha dado permiso explícito para procesar información personal para un fin determinado. Por ejemplo, si completa uno de nuestros formularios de comunicación, le solicitaremos su consentimiento si quisiéramos utilizar su información personal para cualquier otro propósito. Usted tiene el derecho de retirar este consentimiento en cualquier momento. Puede administrar sus preferencias contactando con nuestro Delegado de Protección de Datos en [email protected]. ¿Cómo utilizamos su información personal? Recopilamos información personal por una razón principal, para mejorar y mantener el rendimiento de nuestro sitio web y poder brindarle la mejor experiencia de usuario posible. Recopilamos información personal por dos motivos principales: Mejorar y mantener el rendimiento: para proporcionarle la mejor experiencia de usuario posible, debemos asegurarnos de que nuestros productos y servicios funcionan como deberían ser. Comunicar cambios y ofertas de productos: queremos que obtenga el máximo rendimiento de nuestros productos o servicios, incluyendo mostrar nuestros últimos contenidos y boletines informativos. Puede cambiar sus preferencias en cualquier momento contactando a nuestro oficial de privacidad a [email protected]. ¿Con quién compartimos su información personal? No divulgamos su información personal a ningún tercero a menos que lo exijan las leyes aplicables, órdenes judiciales u otros procesos legales válidos. ¿Cuánto tiempo conservamos su información personal? Un resumen de la duración de su información personal: Categoría de datosEjemploPeríodo RetenciónJustificación del Período Comercial Clientes Hasta 5 años después de la resolución de cualquier relación comercial Para informar de nuestros productos y servicios Comercial Formulario de contacto Hasta 5 años después de la resolución de cualquier relación comercial Para informar de las peticiones realizadas por el usuario Marketing Newsletter Hasta que exprese su negativa a que sea enviada Para informar de nuestros productos y servicios Los datos se almacenarán el tiempo estrictamente necesario exclusivamente para el desempeño de sus competencias legalmente establecidas. A veces es necesario que guardemos su información personal por períodos más largos, por ejemplo: Si existe un requisito legal para retenerlo; Si requerimos la información por razones legales o existe una necesidad legítima para que la retengamos; Para garantizar que no nos comuniquemos con usted si nos ha pedido que no lo hagamos. ¿Cómo mantenemos su información personal segura? Contamos con las medidas de seguridad técnicas y organizativas adecuadas para garantizar que la información de nuestros usuarios esté protegida contra el acceso, uso, alteración o pérdida no autorizados o accidentales. Sus derechos Según las leyes de protección de datos, tiene derechos en relación con sus datos personales que gestionamos. Estos derechos incluyen: El derecho de oposición al márquetin directo; El derecho de acceso a los datos personales que procesamos sobre usted; El derecho a solicitar la eliminación de sus datos personales; El derecho a solicitar la rectificación de sus datos personales. Puede ejercer estos derechos contactando a nuestro oficial de Privacidad en [email protected]. ¿Dónde se aplica esta política de privacidad? La información personal recopilada por el CLIENTE. Nuestro sitio web puede contener enlaces a sitios web de terceros que no están sujetos a esta política de privacidad. No somos responsables de su contenido, uso de información personal o prácticas de seguridad. Si tiene una consulta sobre el tratamiento de su información personal, comuníquese con nuestro oficial de Privacidad en [email protected]. Cambios en esta política de privacidad Esta política es efectiva desde el 24/05/2018. Cualquier cambio que hagamos a esta política de privacidad se publicará en esta página, explicitando la fecha del último cambio.
[ ... ]What is Bitcoin Halving and how does it affect the cryptocurrency?
25/02/2024The term "Halving" in the context of Bitcoin refers to a scheduled event in the cryptocurrency protocol, in which the reward for mining blocks is reduced by half. This event occurs approximately every four years and has a significant impact on the supply and demand of Bitcoin. During Halving, the number of new Bitcoins created per block is halved. This implies a decrease in the issuance rate of the cryptocurrency, which in turn can have an effect on the price and volatility of Bitcoin. Many analysts and experts are speculating about the long-term implications of the Halving and its influence on the cryptocurrency markets. Services related to Bitcoin Halving There are various types of services and tools related to Bitcoin Halving that can be beneficial for different actors in the cryptocurrency ecosystem. These services include: 1. Halving analysis and forecast This type of service provides detailed information about the past, present and future of the Bitcoin Halving. Through analysis and forecasting, it helps investors and cryptocurrency enthusiasts make informed decisions on how to position themselves before and after the event. 2. Bitcoin Mining As the reward in Bitcoin decreases, mining this cryptocurrency becomes more challenging. Bitcoin mining services offer solutions and advice to maximize mining efficiency and profitability, even in a low reward environment. 3. Financial advice related to Halving As the issuance rate of Bitcoin slows, investors may need to adapt their investment strategies. Financial advisory services specialized in cryptocurrencies and Bitcoin provide personalized recommendations and analysis to optimize investment performance in this context. 4. Development of tools for cryptocurrencies The Bitcoin Halving may generate changes in the cryptocurrency ecosystem, which may require the creation of new tools and solutions. Companies specialized in software development and applications related to cryptocurrencies can provide development and consulting services to adapt to these new demands. Bitcoin: Reward Reduction and Its Implications on the Cryptocurrency Ecosystem Bitcoin, the most famous and valuable cryptocurrency in the world, has periodically experienced an event known as a "reward reduction" or "Halving", which has significant implications on the cryptocurrency ecosystem. In this article, we will explore in depth what Bitcoin reward reduction is and how it affects both miners and investors. What is Bitcoin reward reduction? Bitcoin reward reduction is a scheduled event integrated into the cryptocurrency protocol. It occurs approximately every four years and consists of a halving of the reward miners receive for validating transactions and adding new blocks to the Bitcoin blockchain. Originally, when Bitcoin was launched in 2009, miners received a reward of 50 Bitcoins for each block mined. However, due to the reward reduction process, this amount has decreased over time. In 2012, it was reduced to 25 Bitcoins per block, in 2016 to 12.5 Bitcoins per block, and in 2020 it was reduced again to 6.25 Bitcoins per block. Implications for Bitcoin miners Bitcoin's reward reduction has a significant impact on mining the cryptocurrency. With each reduction, miners receive fewer Bitcoins for their work, which means less direct monetary reward. This may result in some miners leaving the Bitcoin network, especially those with higher electricity and mining equipment costs. On the other hand, those miners who manage to adapt and remain profitable even with a lower reward are rewarded with a larger share of the Bitcoin supply generated through mining. This concentration of Bitcoins in the hands of fewer miners can have effects on the decentralization and security of the network, since the number of active participants in the transaction validation process is reduced. Implications for investors and the price of Bitcoin Bitcoin's reward reduction also has implications for the price and supply of the cryptocurrency. As the issuance of new Bitcoins decreases, the supply in the market reduces. This may lead to higher relative demand if Bitcoin demand continues to grow or remains stable. In previous reward reduction events, a long-term increase in Bitcoin price has been observed. This is because the decrease in the supply of new Bitcoins can lead to greater perceived scarcity and therefore an increase in their value. However, it is important to note that the price of Bitcoin is highly volatile and can be influenced by a variety of external factors, so a continued increase after reward reduction cannot be guaranteed. Bitcoin's reward reduction is a key event in the life of the cryptocurrency and has implications for both miners and investors. As the number of new Bitcoins generated is halved, miners must adapt to remain profitable and the supply of Bitcoin on the market may decrease. However, this event can also have a positive impact on the price of Bitcoin in the long term. It is important to understand and take these factors into account when evaluating investment potential in Bitcoin and the cryptocurrency market in general. Bitcoin and limited supply: a unique combination Bitcoin has captured the attention of the financial world like no other cryptocurrency. One of its most notable features is its limited supply, meaning that only a finite number of bitcoins will be created in the world. This contrasts with traditional fiat currencies, which can be printed at the discretion of governments. How does Bitcoin limited supply work? Bitcoin was designed to have a total supply of 21 million coins. As new blocks are mined by users and added to the Bitcoin blockchain, new coins are generated and distributed as rewards to miners. However, this reward is halved in an event known as "Halving", which occurs approximately every four years. Halving ensures that the rate of issuance of new bitcoins decreases over time, following a predictable mathematical function. Currently, the reward per mined block is 6.25 bitcoins, but this number is expected to reduce further in the future. This controlled scarcity mechanism is a central part of Bitcoin's monetary policy. Advantages of Bitcoin Limited Supply Bitcoin's limited supply has several significant advantages: Sense of scarcity: The limitation in the supply of Bitcoin makes it a scarce and valuable asset. As it approaches its maximum supply, demand and price are expected to increase. Inflation Protection: Unlike fiat currencies, Bitcoin cannot be inflated or devalued at the discretion of governments. Its limited supply protects it from inflation and makes it a safe store of value. Monetary stability: With carefully controlled supply, Bitcoin offers greater monetary stability compared to national currencies, which can be affected by political and economic decisions. Challenges and debates surrounding the limited supply of Bitcoin Despite the advantages, Bitcoin's limited supply has also generated debates and challenges. Some argue that the scarcity of bitcoins could hinder its mass adoption as an everyday currency. Price volatility is also an issue of concern. Furthermore, the fact that only about 80% of all existing bitcoins have been mined raises questions about how the latest bitcoins will be distributed and how this will affect the network and its sustainability in the future. Bitcoin has revolutionized the financial world with its limited supply and unique monetary policy. Controlled and predictable scarcity is an essential part of its design, providing a solid alternative to traditional fiat currencies. Although limited supply can pose challenges and debates, it also offers significant benefits, such as a sense of scarcity, protection against inflation, and monetary stability. As Bitcoin continues to mature and its supply approaches its maximum limit, its value and relevance in the financial world continues to grow, leaving investors and enthusiasts with great anticipation about its future.
[ ... ]Lenovo
LenovoFounded in 1989, the Chinese company Lenovo is today another of the world's technology giants. By the beginning of 2021, Lenovo was the largest seller of personal computers in the world by units, and, to give more scandalous data, since 1995 they have sold more than 500 million PCs worldwide. It's not all about PCs. Lenovo also designs, develops, and manufactures tablets, smartphones, workstations, servers, supercomputers, electronic storage devices, IT management software, and smart TVs from operating sites around the world.
[ ... ]Logitech
LogitechSince its inception, the Swiss company Logitech has focused on designing and manufacturing innovative and quality solutions for people's daily lives. Since 1981, Logitech creates and produces computer accessories such as keyboards, mice, speakers, and headsets from production subdivisions in different parts of the world. Through extensive pre-design studies, they analyze how people connect and interact with the digital world. Based on the information gathered, they then design the best products to improve the user experience.
[ ... ]
Patch Panels
If you want to buy a patch panel in our store you will find a large selection of this type of patch panel with which you can easily manage your structured network cabling and ensure a clean signal path to all your connected devices.
[ ... ]Speed Test
Check your internet speed and latency with this test and find out how good your connection is. Compatible with Fiber and ADSL connections. With our speed test, you can assess the quality of your connection quickly and reliably. This test does not only allow you to determine your upload and download speed but also the latency, i.e., the amount of time it takes for a packet of data to travel from one designated point to another. Besides, you can use it to find out the ASN of your internet provider and which IP protocol version you are using (IPv4 or IPv6). To check your internet speed and the rest of the parameters, just click on "Start Test" and, within a few seconds, you will be able to see a summary of the results on your screen. In addition, while the speed test is running, a real-time graph will show you how your connection is performing. For an optimal measurement, it is recommended to use a cable connection, rather than a Wi-Fi or PCL one. Likewise, it is advised to stop any ongoing downloads on the computer on which the internet speed test is running or on any other computer connected to it.
[ ... ]Meta warns about the vulnerability in password recovery linked to the recycling of phone numbers
22/02/2024Meta, a leader in social media, has announced that it will not assume responsibility for personal account theft on Instagram and Facebook related to password recovery through the use of recycled phone numbers. The company argues that it lacks control over telecommunications providers and users involved in this practice. Phone number recycling: an overlooked risk in a recent statement Meta revealed its inability to manage personal account thefts that occur when phone numbers are recycled by telecommunications carriers. This common practice among mobile phone companies involves reassigning discarded numbers to new customers, making them owners of a number previously used by another user. In countries like Spain, carriers wait for a period of 30 days before reassigning a number, but the risk persists if users do not unlink the number from digital services or associated platforms, such as social networks and emails. The danger of not unlinking phone numbers from digital accounts When users deactivate a phone number, whether due to a change of carrier or any other reason, carriers must wait before reassigning the number. However, failure to unlink this number from digital services can result in unauthorized access to personal accounts. In many services, linking the phone number is allowed for actions such as resetting passwords. Users, upon receiving a verification code on their number, can complete the login without the need for email validation or a password. This process, though accepted, can lead to unintentional unauthorized access. Meta warns users about the importance of unlinking phone numbers from digital accounts when deactivating them, insisting on the need to update associated information to prevent account theft.
[ ... ]
Stylus pens
Find the most convenient stylus pen to get the most out of your device's touch screen. A stylus or digital pen allows you to draw, sign documents, take notes, and much more in a more agile, easy, and precise way than with your finger. Try it!
[ ... ]Chat with RTX by Nvidia: Localized customization of chatbots without Internet
19/02/2024Nvidia introduces an innovative tool in the chatbot realm called Chat with RTX, designed for the personalization of conversational assistants. Powered by generative Artificial Intelligence (AI), Chat with RTX operates locally on computers with GeForce RTX Series 30 graphics cards running Windows 10 or Windows 11. Chat with RTX and the IA revolution for chatbots This decentralized approach eliminates the reliance on an internet connection for chatbot functionality. Unlike many conventional virtual assistants, which require constant cloud connectivity for processing and generating responses, Chat with RTX operates internally on the user's device. According to Nvidia, this feature not only enhances privacy by avoiding the transmission of sensitive data over the network but also provides a quicker and more efficient response. With Chat with RTX, users can create personalized chatbots in the style of ChatGPT, Gemini or Copilot for conversational queries. This format allows the incorporation of YouTube videos, text in different formats, and URLs for contextual queries. Nvidia's tool is optimized to leverage the capabilities of computers running Windows 10 or 11 with a GeForce RTX Series 30 GPU and 8GB of video random access memory (VRAM).
[ ... ]MSI
MSIMSI GAMING, is a leading brand of high-end hardware for the demanding world of video games and eSports. Supported by the spirit of gaming, MSI creates and manufactures innovative gaming equipment to nurture its ever-growing community of adept gamers, always open to encourage gamers around the world to network and share their collective gaming wisdom. At MSI, they remain faithful to apply all the latest developments in design and technological innovation, to achieve that extreme performance so sought after and appreciated by gamers.
[ ... ]Netgear
NetgearNetgear, founded in 1996 and headquartered in California, is a multinational computer networking company. Its specialty is the production of networking hardware and accessories to help all types of consumers, businesses, and service providers get the best and fastest possible connectivity. In other words, it helps everyone. Netgear products are designed and manufactured to make the user’s life easier and to ensure that his/her connection is of the best possible quality because no technology is valid if it is not accessible and efficient.
[ ... ]Arc Search, AI-powered search engine for iOS
05/02/2024The Browser Company has introduced its latest innovation to the market, Arc Search, a search engine exclusively designed for iOS devices that integrates artificial intelligence and private browsing functionalities. Arc Search promises seamless and interruption-free navigation, free from annoying ads. Driven by artificial intelligence, this search engine offers, also, advanced features such as the ability to summarize visited web pages and provide search results more efficiently. Additionally, it stands out for its ad blockers, a reading mode that minimizes distractions, and a keyboard designed to initiate searches with just a few taps. In addition to Arc Search, in the spring, The Browser Company will also launch its web browser ARC, based on Chromium, with the ambition to challenge the supremacy of Google Chrome. With these releases, The Browser Company has explained that it aims not only to establish itself as a robust option in the realm of browsers and search engines but also to redefine how users interact with information on their iOS devices.
[ ... ]Where to watch the Champions League on TV or Streaming?
13/06/2023Find out where you can watch the Champions League so as not to miss a minute of this excellent competition that this year again promises good soccer and maximum excitement. When does the Champions League 2021/2022 start? The UEFA Champions League Group Stage starts in mid-September. The first match day will be played on Tuesday, September 14, and will feature Sevilla, who will face RB Salzburg in the Andalusian capital; Villarreal, who will play at home against Atalanta; and FC Barcelona, who will face Bayern Munich, also at home. The following day, on September 15, the 2021/2022 Champions League will kick off for Atlético de Madrid, who will play against Porto at the Wanda Metropolitano, and also for Real Madrid, who will play their first match against Inter, in Milan. This first Group Stage will have six matchdays in which the 32 teams participating in this edition of the Champions League will face each other in home and away matches that you will be able to follow both on television and streaming. Group stage September 14/15, 2021: first matchday September 28/29, 2021: second matchday October 19/20, 2021: third matchday 2/3 November 2021: fourth matchday November 23/24, 2021: fifth matchday December 7/8, 2021: sixth matchday Once the six matchdays of the group stage have been completed, the competition will continue with the knockout phase, which will determine the two teams that will play in the UEFA Champions League final. Knockout Phase Round of 16: February 15/16/22/23 and March 8/9/15/16/16, 2022 Quarter-finals: 5/6 and 12/13 April 2022 Semifinals: May 26/27 and 3/4, 2022 Where to watch the Champions League on TV? As with LaLiga Santander and Liga SmartBank, Movistar has exclusive rights to the UEFA Champions League in Spain until 2024. However, following an agreement with Orange, Movistar has decided to share the rights with this operator, so that in Spain this season the Champions League can be watched on TV on Movistar and Orange TV. In both cases, the broadcasting of the UEFA Champions League group stage matches as well as those of the knockout phase and the Final will be included. How to watch the Champions League on Orange TV? Although Orange does not have direct rights to the Champions League in Spain, its agreement with Movistar allows its customers to watch live Champions League matches on Orange TV. These broadcasts are exclusively for the operator's customers who have the Orange Love Total package, which includes the UEFA Champions League, Liga Santander, and Liga SmartBank matches, in addition to the UEFA Champions League. How to watch the Champions League on Movistar? To watch the Champions League on Movistar we must be customers of this operator and have contracted the Fusión Selección Champions or Fusión Selección Plus con Fútbol package, which also includes the Liga Santander and Liga SmartBank matches. If our package is Fusión Selección con LaLiga, we will only have access to the Spanish football competition and we will not be able to watch the Champions League matches. The Movistar channel on which the Champions League can be watched is called " Movistar Liga de Campeones". "Movistar Liga de Campeones" is an exclusive TV channel for watching soccer and in addition to the UEFA Champions League, it also provides coverage of the Europa League.The schedules of all broadcasts can be consulted in the Sports section of the Movistar+ menu, for ADSL and Fiber TV customers. Where can I watch the Champions League live on the Internet? Both Movistar and Orange complete their Champions League soccer offer on TV through their online platforms. In both cases, to enjoy soccer on our mobile devices or computer, we must be subscribed to a package that includes the UEFA Champions League (in Movistar, Fusión Selección Champions or Fusión Selección Plus con Fútbol, and in Orange TV, Love Total). If you are a Movistar customer and have one of these packages, you must activate Movistar+ on your devices (formerly Yomvi) and you will have access to watch the Champions League online matches on Movistar as well as other online content and series, at no additional cost from anywhere and on any device. All broadcast schedules can be consulted in the Sports section of the Movistar+ menu on any device. To watch the Champions League online on Orange, you must log in to the Orange TV website to identify yourself as a Love Total member. Once we have logged in, we will be able to watch live matches of the UEFA Champions League, LaLiga Santander, LaLiga SmartBank, and also watch matches that have already taken place. Where can I watch the Champions League from outside Spain? If you are a Movistar or Orange customer, the best option to watch the Champions League from abroad is through Movistar+ on your devices or the online platform of Orange TV. If you have problems viewing the matches due to a geographical block, the best option, in this case, is to connect to a VPN with a Spanish IP beforehand. If your Internet access provider does not offer this service, here are the best VPN offers to surf safely (both from home and when traveling). In addition, and depending on the country you are in, various television stations and operators have the broadcasting rights to the UEFA Champions League: Europe Albania: Tring, RTSH Armenia: Vivaro Austria: ServusTV, Sky Austria Azerbaijan: CBC Sport, Saran Belarus: UEFA.tv Belgium: Proximus, RTL, VTM Bosnia and Herzegovina: Arena Sport Bulgaria: A1, bTV Croatia: HRT, Arena Sport Cyprus: CYTA Czech Republic: Nova, Voyo Denmark: NENT Group Estonia: Viaplay Finland: MTV France: Canal+, BeIN Georgia: Adjara, Silknet Germany, DAZN Greece: MEGA, COSMOTE TV Hungary: Sport1, MTVA Iceland: Viaplay, Syn Republic of Ireland: Livescore, Virgin Media, RTE Israel: The Sports Channel Italy: Amazon, Mediaset, Sky Italia Kazakhstan: QazSport, Q Sport League, Saran Kosovo: Arena Sport, Artmotion Kyrgyzstan: Saran, Q Sport Latvia: Viaplay Lithuania: Viaplay Luxembourg: RTL, Proximus Malta: Melita, PBS Moldova: Setanta, Prime Montenegro: Arena Sport Netherlands: RTL, Ziggo Sport North Macedonia: Makedonski Telekom, Arena Sport, MTV Norway: TV2 Norway Poland: Polsat Portugal:Eleven Romenia: Clever Media, Digisport, Telekom Romania Russia: Match TV Serbia: Arena Sport Slovakia: Markiza, Voyo Slovenia: Sportklub, Pro Plus Spain: Telefonica, Orange TV Sweden: Telia Switzerland: blue+, CH Media Tajikistan: Varzish TV, Saran Turkey: EXXEN Turkmenistan: Saran Ukraine: Megogo UK: BT Sport Uzbekistan: MTRK Africa and Middle East Nigeria: SuperSport South Africa: SuperSport Middle East and North Africa (Algeria, Bahrain, Chad, Djibouti, Egypt, Iran, Iraq, Jordan, Kuwait, Lebanon, Libya, Morocco, Oman, Qatar, Saudi Arabia, Sudan, Syria, Tunisia, United Arab Emirates, Yemen): beIN Sub-Saharian Africa: Canal+, SuperSport America Bolivia: Televideo Brazil: SBT, Turner Canada: DAZN Caribbean: Flow Sports, Sportsmax Central America: ESPN Costa Rica: Teletica Dominican Republic: Televideo Ecuador: Televideo El Salvador:Canal Dos Guatemala: Televideo Haití: Canal+ Honduras: Televicentro South America (except Brazil): ESPN Mexico: Turner Panama: TVN, Medcom Paraguay: Televideo Peru: Televideo United States: CBS, TUDN Deportes Venezuela: La Tele Tuya Asia and Pacífic Australia: STAN Brunei: beIn Cambodia: beIn China PR: PPTV, Tencent, iQIYI, Alibaba Hong Kong SAR: beIn India and Indian subcontinent: Sony Indonesia: SCTV Japan: Wowow Republic of Korea: SPO TV Laos: beIn Macau SAR: TDM Malaysia: beIn Mongolia: SPS Myanmar: TBA New Zealand: Spark Pacific Islands: Digicel Philipines: Tap TV Singapore: beIn Taiwan/Chines Taipei: Elta Thailand: beIn Vietnam: FPT Moreover, if you are one of those who can't miss a single live match, you should know that the Sport24 platform has the rights to broadcast Champions League matches on airplanes and cruise ships. Where to watch the final match of the Champions League 2021/2022? The 2021/2022 Champions League final will be held at the Gazprom Arena in St. Petersburg, Russia, on May 28, 2022. Like the rest of the competition, you can watch the Champions League final on TV through Movistar-Movistar Liga de Campeones dial 50 and Orange TV. Where to watch the Champions League 2021/2022 final on the Internet? In addition to television, you can also watch the Champions League final online. In this case, you must also be a Movistar or Orange customer and connect to Movistar+ on devices (former Yomvi) in the first case or to the online platform of Orange TV, if you are an Orange customer to enjoy the match in which the best European soccer team 2021/2022 will be proclaimed. How can I watch LaLiga soccer matches from abroad? If you have already contracted a television service with the LaLiga package and due to a geographic blocking of your television provider and your connection you have problems viewing the matches, the best option, in this case, will be to use a VPN that assigns you an associated IP that is not blocked. If your Internet access provider does not offer this service, below are the best VPN offers to surf safely from anywhere.
[ ... ]Ngs
NgsSince 1996 the Basque company NGS has been fighting hard in the computer peripherals and consumer electronics sector, manufacturing products focused on design and quality. In just 30 years NGS has managed to become a reference in its sector, with high-end products, innovative technology, and an attractive design, while remaining competitive.
[ ... ]The Neeva search engine fails and shuts down
02/06/2023After months of efforts, Neeva, the search engine designed by two former Google employees that aimed to provide a user-tracking-free and ad-free service, has announced its closure. Since its launch, Neeva has failed to gather a sufficient user base to sustain the project, even after announcing Neeva AI and becoming the first search engine to provide real-time AI-driven answers to most queries. Therefore, today, on June 2nd, Neeva will disappear as a search engine. Its founders will redirect their business to a new area, and subscribers with active licenses will receive a refund for the unused period. Neeva has also announced the deletion of all user data.
[ ... ]QNAP
QNAPThe Taiwanese company QNAP (Quality Network Appliance Provider), has been one of the leading brands in data storage servers since its inception in 2004. Despite its short lifespan, QNAP has managed to gain a foothold in international markets thanks to its comprehensive solutions in software development, hardware design and in-house manufacturing. Focusing on storage, networking and intelligent video innovations, their products stand out for their usability, high storage capacity, security and reliable fast data access from anywhere in the world and on any device.
[ ... ]Apple, Google and Mozilla will create a speedometer to evaluate Safari, Chrome and Firefox
20/12/2022Apple, Google and Mozilla start a joint project to develop Speedometer 3, a speedometer that is going to be useful to use to analyse and improve the performance of Internet browsing programs. The new speedometer will measure the responsiveness of web applications, timing user interactions across various workloads. In addition the three companies has explained that Speedometer 3 will be useful for adjusting any component to its maximum speed, although, according to the agreement signed by they three, any of their respective browsers, Apple's Safari, Google's Chrome or Mozilla's Firefox, can make significant changes to their performance until have the approval of the other two companies.
[ ... ]Samsonite
SamsoniteIf suitcases have a reference brand this is undoubtedly Samsonite. Samsonite, is an American multinational, which since 1910 has not stopped innovating in the world of premium traveling luggage, design and resistance. Samsonite suitcases and travel items have been evolving constantly, and its designs and creations have provided products that have taken the market by storm throughout its long history of life.
[ ... ]Totto
TottoTotto is a leading company in the design of bags, accessories that fuse fashion and functionality. Undoubtedly, its collection of laptop backpacks is a clear example of this. Since its creation in 1958, Totto has had a long history of success offering its customers original design products and quality items. Since its beginnings in Colombia, its mission was to quickly develop a brand that made products focused on combating the idea that practicality in travel bags and backpacks for carrying electronic devices has to come hand in hand with excessive elegance.
[ ... ]The European Commission spends �400,000 on its own metaverse and only attracts six people to the inauguration
05/12/2022Absolute failure. The inagurated of the new metaverse from the European Commission that was presented a few days ago with a virtual party, only attract six persons. According to the specialized journalist Vicen Chadwick from Devex, the European Commission has invested €387,000 in the project to develop a virtual world, designed to attract the attention of young people and create a shared space on the Internet in which they can become aware of those thinghs that EU does on the world stage, and reflect on the problems that affect a globalized world. Also, this metaverse is designed to promote actions of the European Union related to health, education, climate and other topics of interest for youngest, such the Erasmus scholarships. The inauguration of the space, however, went completely unnoticed by the target audience and the few persons who entered the party, such as the journalists from Gizmodo, assure that the metaverse of the European Commission has many shortcomings.
[ ... ]TP-Link
TP-LinkTP-Link is a global provider of networking equipment. The company was founded in China in 1996 and, since then, has built a portfolio of products that meet the networking needs involved in all aspects of everyone's daily life. If there is one thing that defines its products, it is that they are designed and built to deliver stability, performance, and value to both consumers and businesses.
[ ... ]The new USB 4 2.0 promise speeds up to 80 Gbps for data transfer
19/09/2022Next for his market presentation, the main characteristics of the new generation of USB are already known: USB 4 2.0 promises to double the speed of Thunderbolt 4 and the original USB 4.Although we will have to wait until November to know all their technical characteristics, USB Promoter Groupt has already explained that USB 4 2.0 will offer speeds up to 80 Gbps for data transfer, through a USB-C cable and connector.This significant increase in transfer speed is possible because the new USBs incorporate a new physical layer architecture, capable of supporting. So, the new USB are preparing, for example, to support the transfer of 4K or 8K videos from one computer to another without problems or to offer, also, the maximum gaming experience to gamer users thanks to its ultra-fast speed rate.Intel, meanwhile, is already working on Thunderbolt 5, which everything indicates will also offer speeds of 80 Gbps.
[ ... ]Ubiquiti-networks
Ubiquiti-networksUbiquiti, is an American multi-brand technology company that since its inception in 2005 has created and manufactured products to provide connectivity solutions to homes and businesses around the world. Ubiquiti's products are designed to meet the needs of its customers and give the best service performance. Ubiquiti's wide range of products is designed to facilitate wired and wireless data communication and optimize network performance and organization.
[ ... ]Samsung launches a microSD card that can record data for 16 years in a row
09/05/2022The new Samsung Pro Endurance microSD card that multiplies the normal life cycle of memory cards by more than 30 times, is now on sale. Samsung Pro Endurance can work continuously 140,160 hours or what is the same, 16 years, a period significantly higher than the average life of 5 years of a standard microSD card. Exclusively designed to cover the needs of video surveillance cameras, the memory card offers enhanced endurance and superior performance for continuous, smooth and reliable capture and playback. “Both consumers and business users can rest assured that our new memory card will ensure continuous recording in high resolution, even under extreme conditions,” said KyuYoung Lee, Vice President of Memory Brand Product Biz, Samsung Electronics Team. Samsung's new memory card offers read and write speeds of up to 100MB/s and 40MB/s, respectively, and a rated Video Speed Class 10 up to U3 and V30 According with Samsung, this makes this micro SD card ideal for handling large high-resolution files while allowing perfect Full HD and 4K recording and playback. The new Samsung Pro Endurance microSD is available in four different storage capacities, 32GB, 64GB, 128GB and 256GB.
[ ... ]How to know if Pegasus has infected our mobile
05/05/2022The news of recent weeks, in which it is claimed that the Pegasus espionage program has been used to enter the mobile devices of Spanish politicians, has put a lot of people on alert. Pegasus is a malicious software that, once introduced on a device, has the ability to collect information and transmit it to an external entity without the consent or knowledge of the owner of the device, be it a mobile phone, a computer or a tablet. Pegasus also erases its trail after it is installed. Among its main features, it also stands out that Pegasus is capable of detecting who the owner of the device has been with. Pegasus also, can send and recive messages autonomously and recording conversations by manipulating the attacked mobile, computer or tablet. The two ways that this spy program uses to enter on a devices is through an SMS or a fraudulent link and, according to experts, despite the fact that it is a very difficult spyware to detect, there are some signs that can make us suspect that we have been infected. Overheating or slowdown of the system are two of the main ones, but also the fact that the battery life is decreasing or that there is excessive data consumption when we are not using the device. How to make it difficult for Pegasus To try to avoid being infected by Pegaus or by any other malware, the director of Systems Engineering at Fortinet from Spain and Portugal, José Luis Laguna, in statements collected by Europa Press, recommends taking extreme precautions and a make a double-checking when personal and confidential information is provided. In addition, the Fortinet expert explains that instead of clicking on the link that we have received, to verify that it is legitimate, it is recommended to write the address of the site in the web browser, even though this means taking an additional step and not accessing directly to this service. Using protection 'software' based on behavior - EndPoint Detection and Response (EDR) -, keeping the system updated, avoiding public Wi-Fi connections and checking the permissions granted to applications, are other precautions that are also recommended.
[ ... ]Island Browser for Business Reaches $1.3 Billion Value
06/04/2022Just some weeks after its launch, Island, the webbrowser focused in enterprise and security, has just reached a $1.3 billion valuation. Island browser is based on chromium and has been developed by two former Symantec executives, who were looking for an option configured to the web security needs of companies and not conventional users. The new browser, in addition to limiting the add-ons that many often some people install on company computers and that sometimes cause significant security breaches, incorporates specific tools to prevent this type of actions, protect SaaS applications, identify incidents and prevent data theft. Depending on the level of security required by each company, Island Browser allows, for example, to download content or not, disable or enable the copy and paste option or deny access to certain domains, among other options. From Island, also insist that their project is based on the utility and not on the consumer, so that the characterization level of Island browser it offers the minimum.
[ ... ]Recycling containers connected to the mobile to reward the citizen
31/03/2022The Spanish startup Recircula Solutions has just presented Recysmart to the market, a device that can be installed in any type of urban container and identify the material of the recycled packages. The objective of this development is to promote incentive programs that helps population to recycle. The device combines a unique mechanical design with AI algorithms based on acoustics, so the unique and characteristic acoustic signal that a package generates when it's inserted into a container is captured by the sensor, processed and reported in real time to the managers authoritys so they can remunerate the person who has use the container. To do this, the citizen will have previously identified himself on the device through his mobile or using a physical card. In Sant Cugat del Vallés (Barcelona) several of these devices have been installed in various containers in the town. Recircula Solutions will also send several units to Portugal, Austria, France, the United Kingdom and Greece.
[ ... ]5G will trigger data consumption that will multiply by three in five years
18/03/2022In 2025, 25% of global data connections will be 5G, compared to 8% at the end of 2021, according to GSMA forecasts, which also indicate that this greater implementation will have a greater impact, even in Europe, North America, China and some Asian countries, where the percentage of 5G penetration would be higher in that date. Among the main consequences of the 5G expansion, will be a greater consumption of data by users, has said GSMA and if, at the moment, the data traffic per smartphone in a month, is 11.4Gb on average, the forecasts by 2027 place it at 41Gb, three times more. And according to the organization that brings together the telecommunications industry and organizes the MWC in Barcelona, as the population has access to 5G, there will be a significant increase in streaming consumption, favored by a sudden drop in download times that will become negligible. The use of remote health services, ultra-high definition television (4K/8K) and 5G as home broadband are also expected to grow.
[ ... ]Android 12 allows you to disable 2G networks on your mobile
26/01/2022The latest version of Google's mobile operating system, Android 12, allows you to disable connections through 2G data networks. To do this, you must deactivate this connectivity through the 'Network and Internet' and 'SIM' sections, where you will find the option “allow 2G”, which you can activate or deactivate according to your preferences at any time. As explained by the Electronic Frontier Foundation (EFF), 2G networks has a very vulnerable encryption system and is quite easy that a hacker intercept the signal and track the exact location of the user. Android reports that despite the fact that 2G connectivity is disabled, this coverage will continue to be available for emergency calls.
[ ... ]Common front against advertising based on user surveillance
19/01/2022Facing the forthcoming vote on the EU Digital Services Law, a group of 17 civil organizations and 14 digital companies have demanded the European Parliament prohibit invasive and hostile practices with privacy that take place in digital advertising such as user tracking. According to his complaint, companies that specialize in monitoring the behavior of Internet users, integrate data from all websites, something that entails a violation of EU data protection regulations. In addition, they remember, these advertising practices make use of "inferred data that reveals vulnerabilities of the users" and, in general, they insist, this data are obtained without the knowledge of the user and beyond their control. The signatories, including the privacy-focused search engine companies DuckDuckGo and Ecosia, denounce also that these types of practices only favor a few “dominant players” based in the United States, and they specifically cite, among others, Facebook and Google. As an alternative to these advertising systems, they propose to follow initiatives such the Dutch television channels NPO and Norwegian TV2, which opted for contextual advertising and increased their income from ads.
[ ... ]Fisher-Price Phone Can Now Make Calls
22/10/2021Seeing is believing, but that's the way it is. Fisher-Price has unveiled a new, smart and fully functional version of the popular 'Funny Face Phone'. The new version maintains the original design and connected to the user's mobile data plan, can make calls in a conventional way. This new version also adds new functionalities such as hands-free with a speaker button. This new "Fisher-Price funny face" phone, with Bluetooth connectivity to pair with an Android or iOS phone, has autonomy for nine hours of conversation on a single charge. And it is "mobile" thanks to its wheels. The launch coincides with the 60th anniversary of this mythical children's phone. The new version is only abaible in the United States, specifically on “Best buy” shops, and its price is 60$.
[ ... ]Facebook announces 10,000 new jobs in Europe to develop its metaverse
19/10/2021Facebook has announced 10,000 new jobs in the European Union to develop a new virtual environment. This environment is going to be design to interconnected virtual experiences using different technologies as virtual and augmented reality. This new environment baptized as a metaverse will increase the feeling to be presence in the virtual environment and the interaction between all those who are there. The goal, explains Vice President of Global Affairs, Nick Clegg, Vice President of Core Products, Javier Olivan is create a greater sense of 'virtual presence', to unlock access to new creative, social and economic opportunities. Facebook will shortly begin recruiting candidates for the 10,000 jobs. Their first priority will be highly specialized engineers.
[ ... ]USB-C cables will be marketed with power rating logos
05/10/2021USB type C cables will be marketed with new logos according to their power, has announced USB Implementers Forum (USB-IF). USB-IF has explained that the new logos have been designed to solve cable confusion and to make it easier to decide which cables and chargers to purchase depending on the costumer needs. This type of cable has options from 60W to 240W. The consortium has also presented through the same statement, the logos for USB 4, based on Thunderbolt and with transfer rates of up to 40 Gbps.
[ ... ]Makeup causes failures in facial recognition systems
22/09/2021A research from the Ben-Gurion University of Israel has concluded that makeup reduces the effectiveness of facial recognition mechanisms. During the tests, the researchers used the ArcFace facial detection system, and they determined an effectiveness of 47,6% in people who did not use make up and 33,7% in those who did. They also confirm that applying makeup in specific face areas that algorithms analyze, the effectiveness of the facial recognition system is significantly altered and only 1.22% persons were recognized. In addition, the researchers from the Israeli university also did the test digitally, making up some photographs of the volunteers and the result was that the system was not able to recognize any of the faces. According to all these results, the researchers believe that the current level of development of facial detection systems is still below the realistic threshold.
[ ... ]Windows 11 ready and with 10 days to roll back to the previous version if you do not like it
14/07/2021Everything is ready so users can begin to install Windows 11 before the end of the year with the great added novelty that if once the update is installed but it does not convince you, you can roll back to the previous version. Microsoft said that Windows 10 users who upgrade to Windows 11 will have 10 days to easily roll back that update. After that 10-day grace period you will need to back up your data and do a 'clean install' to move back to Windows 10. The possibility of upgrading to Windows 11 will depend on the compatibility of the computer with the new version, although in a document of questions and answers for the commercial ones, Microsoft indicates that most of the Windows 10 computers that at the moment are commercialized fulfill the minimum requirements to do it. In the same document, Microsoft explains that Windows 11 maintains the performance and security of Windows 10 "with a redesigned and refreshed look and feel," and new tools, sounds and applications. It is also confirmed that Windows 10 support will be maintained until October 14, 2025.
[ ... ]Macro cyber-attack affects more than 350 companies worldwide
07/07/2021The number of companies that have suffered from the REvil macro cyberattack now exceeds 350 organizations worldwide from which the cybercriminals are demanding 70 million in bitcoins to provide them with a universal decryptor to restore their data. The attack was conducted through the update system of IT services software company Kaseya, which REvil exploited to spread and hide ransomware. The virus was leaked to TI Kaseya resellers and from there has reached all end customers using their software. The official data provided by TI Kaseya sets the number of affected companies at 350, although other sources such as the cybersecurity company ESET talk about more than 1,000, including some Spanish organizations, although no names have been disclosed. It has been made public that one of the companies most affected by the cyberattack has been the Swedish supermarket chain Coop, which has had to close its more than 800 points of sale for a few days due to the impossibility of using its cash registers or charging customers. Based on Sophos threat intelligence, REvil has been active in recent weeks and is currently the dominant ransomware gang involved in Sophos' defensively managed threat response cases. Prior to this latest attack, they were also responsible for the one suffered by meat company JBS, which forced the cancellation of all work shifts at the company's slaughterhouses in the US. JBS paid up to 11 million to restore normal operations. These macro cyber-attacks are in addition to other recent and highly significant ones, such as the one perpetrated by the hacker group DarkSide, which forced the preventive shutdown of the largest oil pipeline network in the United States, Colonial Pipeline, endangering the supply of fuel in a large part of the country, or the one suffered by the SEPE and the Ministry of Labor in Spain a few weeks ago.
[ ... ]Atari VCS, Atari's retro mini-console for playing games and enjoying digital entertainment, hits the market
21/06/2021Atari has announced the launch of Atari VCS, its retro mini-console on which they have been working for the last three years and with users will be able to access classic games as well as digital entertainment. Atari VCS is presented as a hybrid console with a videogame console and computer functions inspired by the design of the Atari 2600, as can be seen in the chassis of the equipment, with a matte black body riddled with horizontal stripes and a wooden front. The mini-console is powered by the AMD Ryzen R1606G processor, which streams video in 4K and has support for PC gaming. In this PC mode, the Atari VCS is compatible with operating systems such as Windows, ChromeOS or Ubuntu, features Google productivity solutions and offers the possibility to expand the internal storage. The mini-console, which comes with a joystick and game controller, provides access to a catalog of 100 classic games, streaming entertainment platforms and productivity tools. It can also be connected to a TV and has access to Antstream or Game Jolt libraries, and to different computer game libraries in PC mode. It also allows viewing content from the most popular streaming and social platforms, such as Netflix, Disney+, Prime Video, Facebook, Twitter, Twitch ... Atari VCS is now available for pre-order for $399.99.
[ ... ]How to set up a digital marketing strategy?
16/06/2021As our daily life Internet gains prominence in our physical world, companies selling products and services are increasing their online presence. To do so, they resort to strategies and tactics that ensure their omnipresence in both worlds, with the main task of attracting and retaining customers who buy their products. In this race for customers' attention, strategies such as Inbound Marketing and Outbound Marketing have emerged as protagonists and although they are radically different in their forms, both techniques have found in online communication an ideal medium through which to achieve their goals. What is Inbound Marketing? Inbound Marketing is based on attracting customers through non-intrusive techniques that use content related to the needs and interests of our target audience to attract them to our brand and products. Inbound Marketing Strategy In Inbound Marketing, content is the king and the strategy to get the user to approach the brand is to create, through these contents, links with the customer and establish a relationship of trust and support that favors their interest in our products and services, as well as their loyalty. To achieve this attention on the contents, it is basic and essential to optimize the SEO search engine, which makes our website, our contents and brand visible, makes us relevant and also contributes to our authority. To achieve this optimization and positioning, SEO will be in charge of indicating which words are trending in searches related to our content, will improve the structure of the web to allow a correct user experience, will implement a good strategy of referral links or link building and will take care of other aspects such as the integration of CRM tools or user metrics. All this will make it possible for our content to be positioned and that in a totally "natural" way and without any intrusion, all those contents written according to the interests of a certain group of customers, awaken their interest and attract them to our brand. Inbound Marketing Tools Throughout the whole process of customer attraction and loyalty, the Inbound Marketing strategy has a wide variety of tools to achieve its goal: Blogs Landing page Lead Creation Calls to action Intelligent content Workflows, ... What is outbound Marketing? Unlike Inbound Marketing, outbound Marketing is based on a totally traditional commercial approach, in which the product or service being sold is the only protagonist of the communication. Outbound Marketing Strategy To reach the public, outbound strategies use invasive methods that address broad audiences, without a specific target, with the intention of reaching the maximum number of possible interested parties. Outbound Marketing strategies are based on one-way communication, from the brand to the customer. The company shows the value of its products and services and tries to convince the public to buy them. All this operation is implemented without the customer's request, even before he has made a search or has shown previous interest in a specific product or service. Outbound Marketing Tools In Outbound Marketing, since there is no specific target audience segment, the communication reaches many users, although it may not be of interest to any of them. To achieve this massive distribution, companies use resources such as: Pop-ups Advertisements inserted in videos Banners Email campaigns for which companies use powerful email marketing software in Spanish, with multiple integrated tools that allow from automating mass mailings to A/B testing, comprehensive monitoring of the actions of each recipient (open rate, clicks on links,...) or even advanced segmentation based on interactions and / or user behavior detected in previous actions. Newsletter, inbound or outbound marketing? Now that we know the differences between Inbound and Outbound Marketing, we will finish by looking at a very useful and versatile tool that, unlike those previously mentioned is used interchangeably by both strategies. We are referring to the Newsletters. If we look at the Newsletter of Which is my IP, for example, we would be talking about an Inbound strategy, because to receive the electronic newsletter you must first register (by the way, if you have not done so yet, do not miss it and you will receive timely information on news and updates to get the most out of your Internet connection). On the other hand, if we look at newsletters like the ones we have all surely received at some time, in which we are offered, for example, a telephone offer from a company that is not our own, we are dealing with an electronic newsletter included in the marketing plan of an Outbound strategy. At this point, we can only conclude that knowing our priorities as a company, analyzing the degree of knowledge we have about our target and assessing our objectives, we will have all the necessary answers to start working and designing our digital marketing strategy.
[ ... ]What is the value of a Bitcoin?
11/06/2021Since Bitcoin first appeared in 2009, this digital currency not issued by any government or company, nor, under the umbrella of any kind of economic policy, has gained a foothold in the market and has already started to fit into existing legal frameworks. What gives Bitcoin its value? The great value of Bitcoin is that it is a decentralized and global currency, an alternative to fiat currencies (those issued by governments). All transactions with Bitcoins are public and each of these crypto currencies belongs exclusively to its owner, therefore, it is a currency that cannot be intervened by anyone. What can I do with Bitcoins? To date, with this cryptocurrency, it is possible to monetize all kinds of services, in addition to making investments, free or practically free of commissions, which in the medium to long term are proving attractive. This has made Bitcoin an asset in which to invest and an increasingly popular means of payment through which to transfer value from one user to another without losing friction along the way, going through an intermediary or paying a commission. What is the price of a Bitcoin? Like any other good, the price of a Bitcoin varies according to market demand, although the fact that it has been designed to behave as a deflationary asset and that its supply is limited to 21 million coins, facilitates that by the law of supply and demand itself, the Bitcoin exchange rate tends to rise continuously. As of June 9, at the time of writing this article, the Bitcoin value today is 30,007.86 euros, 3.4 times its price a year ago, when the Bitcoin to Euro conversion rate was 8,629.5 Bitcoins for 1 euro. In 2010 Bitcoin price was less than one Euro cent. What does the value of Bitcoin depend on? The value of Bitcoin depends on the trust and acceptance of users to use it, hence why Bitcoin is rising in value some days and not others. As Bitcoin has been implemented as a means of payment in multiple transactions and its popularity has grown, its value has grown in parallel. Likewise, when there have been news or events that have questioned, for example, the suitability of this crypto currency, its price has fallen. Like any other currency, the price of Bitcoin fluctuates and it is the users themselves who set it at the time of the purchase and sale transaction, which prevents the existence of a single price for Bitcoin, since it is not operated through a single platform as is the case with other currencies. Even so, buying and selling prices of Bitcoins tend to be quite similar. To know how much Bitcoin costs, there are several online platforms, known as "Bitcoin trading platforms" that report live the evolution of the value of the cryptocurrency. Is it safe and profitable to invest in Bitcoin? As with any other asset, investing in Bitcoins is profitable if we know how to do it at the right time. On the other hand, the Blockchain technology on which Bitcoin is based is reliable and difficult to manipulate, with no risk of being counterfeited, although some experts believe that the perfect, 100% inviolable system has not yet been created. In the cryptocurrency segment, convertibility is contemplated, so that Bitcoins can be exchanged for fiat currencies. What can I buy with Bitcoins? Over the last few years, a large number of companies have incorporated Bitcoin as an official method of payment for their goods and services From travel companies to ticket sales platforms for all kinds of shows, through gaming platforms, digital bookstores, software stores or even non-profit organizations already accept this digital currency. That is, Destinia, 13tickets, Gear Best, Shopify, Wordpress, Hostinger, Greenpeace,... among many other companies. eBay is currently considering adding Bitcoin as a method of payment. What is Bitcoin mining and how are Bitcoins generated? The users themselves through a totally decentralized system create Bitcoins. To become a bitcoin creator, computers with high computational capacity are needed to process and verify transactions and quickly solve the complex digital processes of generating the currency. This work is called mining and one of its best attractions is that the system offers "miners" rewards in Bitcoins in exchange for these services, which has made this activity very appealing for certain users. Is it profitable to mine Bitcoins in Spain? Bitcoin mining requires very powerful equipment, with high calculation capacities to solve operations, being nowadays totally inoperative for this operation the PCs of domestic or office use. The investment to mine Bitcoins requires, in addition, to assume the large power consumption required by this more powerful equipment, which makes Spain, at this time due to the high price of KW/h, an uninteresting market for mining Bitcoins. On the contrary, other locations such as China, Iceland, Iran or Georgia, where the Bitcoin mining business is in full expansion, are very interesting.
[ ... ]QUIC, the new official network protocol to replace TCP
04/06/2021QUIC, the network protocol designed by Google, has been presented by the Internet Engineering Task Force, IETF, as a new official Internet standard to replace TCP, the current main standard. Google's QUIC (Quick UDP Internet Connections) network protocol is designed to reduce latency with retransmissions taking less time, potentially reducing the waiting time for search results by 8% on computers and 4% on mobile devices, according to the paper released by Google in 2017. QUIC will replace TCP, the current main standard of the Internet since 1974 - when it was still Arpanet - and on which the operation of Internet elements such as the World Wide Web (WWW) logic system, file transmission, 'emails' and remote administration depend. The new QUIC protocol has already been published by the IETF, making it an official network protocol.
[ ... ]Apple wants to launch its own in-house 5G modems by 2023
17/05/20212023 is the date that most analysts estimate, as likely Apple does, to do the presentation of its first 5G modem. If the forecast comes true and Apple goes ahead with its own 5G modems manufacturing, Qualcomm, the current suppliers of the Snapdragon X55 modems for the iPhone 12 and Snapdragon X60 for the next iPhone 3, would be out of the equation, although the agreement they have signed until 2025 with Cupertino could lead to simultaneous Apple launches in the smartphone market with one or the other modem depending on the region of sale for a while. The development of Apple's 5G modems comes after the company bought the Intel division dedicated to these devices two years ago.
[ ... ]Microclaudia, the Spanish antivirus that makes the attacker think the system is already infected
28/01/2021The National Cryptologic Center (CCN-CERT) and the cyber security company S2 Grup have created "Microclaudia", a tool designed as a vaccine against malware that makes the attacking agent to believe the computer is already infected. "Microclaudia", which can work in parallel to any other protection system already installed on the computer, runs on the system and prevents the attacking of several malwares that are currently in circulation. According to the creators of "Microclaudia", this new antivirus is an important step forward to put an end to the damage caused daily by cybercrime in Spain, the second most common crime, only after theft.
[ ... ]